TL;DR
Client-side security protects the user-facing components of a web application—primarily what runs in the browser—from malicious code injections, third-party script abuse, and data exfiltration. As modern websites grow in complexity, securing the client side is essential to ensure privacy, compliance, and trust.
Introduction
Client-side security refers to the technologies and policies used to protect an end user from malicious activity that is occurring on dynamic web pages accessed from the end user’s own device. It is also sometimes referred to as the “front end” in the context of code development for web applications. Client-side attacks have been increasing in both scale and cost since the beginning of 2020 as companies expand their investment in the end-user digital experience. This has created an unprecedented opportunity for threat actors to exploit end-user activities.

Why do businesses need client-side security?
Modern web applications load an average of 20+ third-party scripts as part of the standard user experience. This ongoing integration and reliance on third-party code creates a software supply chain that is collected and implemented on your customer’s/client’s device, almost in real-time.
The risk that one of these many third-party scripts is housing a security threat is an ongoing concern. The best way to protect your customers from these insidious attacks is to minimize client-side vulnerabilities—a security posture that is often forgotten in favor of boosting server-side security upgrades instead.
Let’s explore the basics of client-side security and discuss how businesses can protect themselves and their customers with automated tools, monitoring, and controls to stop threats, all while safeguarding customer data.
Why is client-side security important?
In cybersecurity, client-side security, client-side vulnerabilities, and client-side attacks refer to security incidents and breaches that occur on the customer’s (or users) computer system rather than on the company’s (on the server side) or in between the two.
To fully mitigate your risk for breaches or attacks, companies must simultaneously protect both their server and the client-side of their business. This includes everything that the customer sees, such as text, images, and the rest of the UI, along with anything the customer interacts with, such as what the website or web application does within the user’s browser. It’s estimated that 98% of the U.S. Alexa 1000 websites do not have the proper protections that can repel a client-side attack.
Client-side vulnerabilities are so prevalent today because the rise of online shopping and experiences have pushed many of our daily transactions online, opening up unprecedented opportunities for threat actors to exploit these vulnerabilities.
Despite its complexity, one of the most important actions any business can take is protecting their customers from client-side security threats, which seek to tamper with the connection between server and client. Unfortunately, because of the sophisticated and subtle nature of these attacks, they can be hard to detect until it’s too late.
To ensure that businesses are offering a safe and secure digital experience, they must be diligent about securing their website or web application from dangerous client-side attacks.
Client-Side Vulnerabilities
To offer a secure experience, companies must ensure that customers can safely access and engage with their digital business. Unfortunately, since there are so many aspects of a web app or webpage that customers can engage with within their browser, there are many possibilities for client-side vulnerabilities that can be exploited.
Here are some of the biggest areas where client-side vulnerabilities are being identified.
Third-Party JavaScript Vendors
JavaScript is an area of great vulnerability for businesses, especially when the source code comes from open-source or third-party providers. Since JavaScript environments do not come with default security permissions, the onus is on businesses and site owners to manage and implement security themselves.
If they do not understand security well or are trusting the third-party provider to set up security on their end, this can lead to concerning vulnerabilities that are easily exploited by bad actors.
Reliance on Form Data
It’s been estimated that 98% of websites use forms to collect personal and financial data from customers. Even though most consumers trust these forms, the personal information collected within them is typically exposed to more than 15 separate third-party domains, increasing the risk for this information to be accessed in a breach.
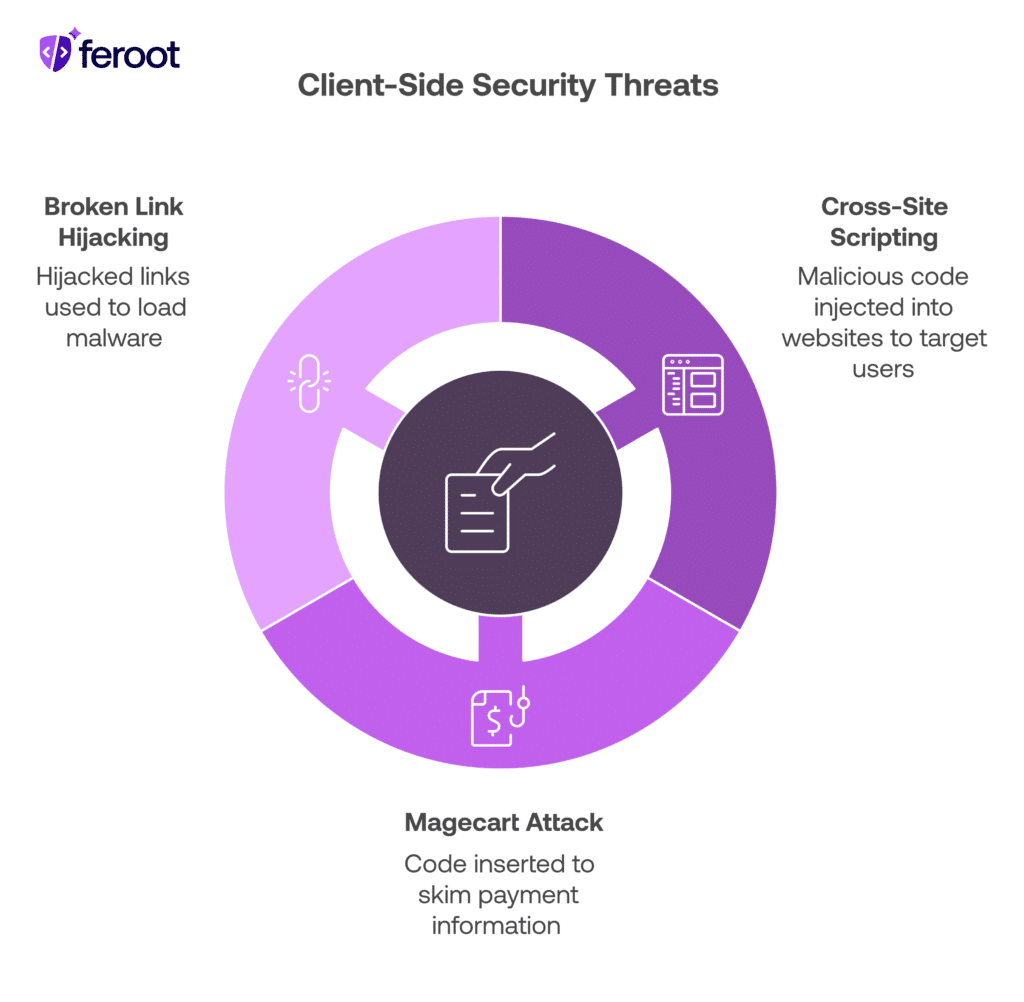
Client-Side Security Threats and Attacks
Even as businesses are shoring up client-side vulnerabilities, bad actors are stepping up their threats and attacks. Fortunately, the most popular of these attacks are well-known.
By educating yourself and your team on the most common client-side security threats, it’s easier to learn how to stop them in their tracks.
Cross-Site Scripting
Taking advantage of cross-site scripting (XSS) is one of the most common ways for bad actors to launch a client-side attack, since estimates show approximately 53% of web applications are affected by this vulnerability.
In a typical XSS attack, malicious code is injected into website content and can target unsuspecting users viewing that site. This threat is so common that it’s regularly on OWASP’s list of Top 10 Vulnerabilities.
Magecart Attack
Another common client-side attack is the Magecart attack, also called payment skimming or e-skimming. It operates using a small piece of code, which is inserted into a website to skim information from customers. Most often, it’s inserted into payment pages, where it acts as an online credit-card skimmer, pulling the personal information and credit card details of anyone who comes across it.
Magecart attacks have become shockingly commonplace. Some of the most well-known businesses that have been affected include:
- British Airways
- Ticketmaster
- Newegg
- Macy’s
Broken Link Hijacking
Companies that are not careful and leave unused, expired, or invalid links on their websites or web applications put themselves at risk for broken link hijacking. This client-side attack relies on companies forgetting about broken links, which are then hijacked and used to load malware or other types of malicious code into the user’s browser.
To protect your company from broken link hijacking, ensure that all links that are no longer valid or in use are removed or replaced immediately.
Client-Side Security Tools
Companies that cannot offer customers a safe browsing experience put themselves in danger of embarrassing reputational damage, as well as costly, time-consuming data breaches. In the case of a major breach, the legal fees, fines, and recovery costs can easily skyrocket into the millions.
Protecting your enterprise from these client-side attacks requires constant vigilance. Fortunately, many companies are now offering sophisticated client-side security tools that can help you identify vulnerabilities and prevent attacks. Whether you proactively enable runtime protection for your JavaScript or simply install monitors that can report on the real-time status of your website or web application, there are lots of ways for companies to stay ahead of client-side security vulnerabilities.
At Feroot, we are passionate about creating intuitive and easy-to-use tools that businesses can deploy in the fight against client-side threats. Two of the tools that we always recommend to our clients are Inspector and PageGuard.
- Inspector digs into your web assets and reports on any client-side security vulnerabilities. It detects and outlines any areas of concern, then immediately provides specific recommendations that developers, security analysts or application security professionals can use to mitigate the issue.
- PageGuard is an automated solution that can protect both websites and web applications in real-time. It automatically applies security configurations and permissions to every page, ensuring the continuous monitoring of all client-side vulnerabilities, including malware and other malicious third-party scripts. It’s a great way to ensure the protection of your customer across the entirety of their user journey.
- DomainGuard is a purpose-built security solution designed to help businesses control their client-side attack surface by deploying and managing Content Security Policies on their web applications. Using automation, DomainGuard identifies all your first- and third-party scripts, your digital assets, and the data they can access. It then generates appropriate Content Security Policies based on scanned data and anticipated effectiveness. Businesses can fine tune their CSPs at the domain level for easy management, version control, and reporting.
Protect Your Customers with Responsive Client-Side Security Tools
Client-side security may be complex, but with responsive, customer-focused tools like Inspector and PageGuard deployed on your web assets, it’s much easier to identify vulnerabilities and repel threats.
Want to learn more about client-side security and how you can protect your enterprise? Request a demo of both Inspector and PageGuard today to explore their robust capabilities first-hand.
FAQ
What is client-side security?
Client-side security is the practice of protecting code, scripts, and interactions that occur in a user’s browser from threats such as malicious injections and unauthorized data collection.
Why is client-side security necessary?
It’s critical to prevent attacks that happen in real time on the user’s device, protect sensitive data, and meet privacy regulations like GDPR and CCPA.
What are examples of client-side threats?
Threats include JavaScript injection, cross-site scripting (XSS), formjacking, clickjacking, and Magecart attacks that target checkout or login forms.
How can companies implement client-side protection?
By using tools like Content Security Policy (CSP), Subresource Integrity (SRI), and real-time JavaScript monitoring to detect and block unauthorized behavior.
Does Feroot help with client-side security?
Yes. Feroot provides solutions that monitor and secure your web applications’ client-side code against active threats, enhancing compliance and user trust.





