TL;DR
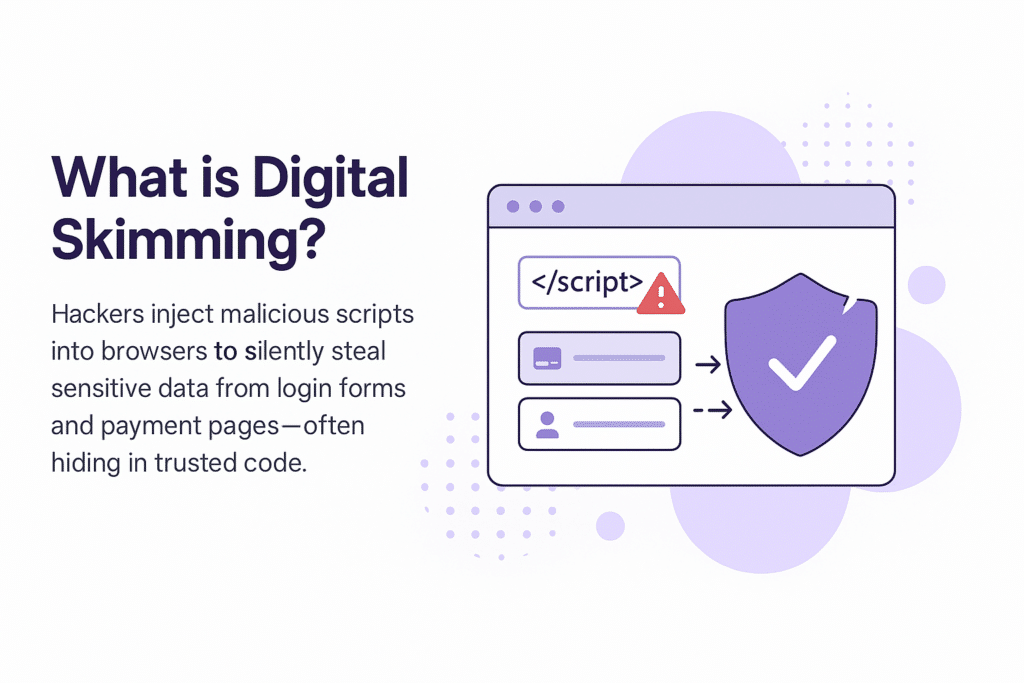
- Hackers inject malicious scripts into browser environments to silently steal sensitive user data.
- These attacks often hide inside legitimate-looking third-party or open-source code.
- User input fields like login forms and payment pages are prime targets for skimming.
- Traditional perimeter and server-side tools can’t detect client-side data exfiltration.
- Without real-time client-side monitoring, organizations risk undetected breaches and compliance violations.
Introduction
Digital skimming is the modern evolution of pickpocketing — but instead of reaching into your back pocket, cybercriminals are reaching into your browser.
For centuries, thieves relied on sleight of hand to steal wallets and valuables in crowded streets. Today’s cybercriminals don’t need physical proximity or manual tricks. With just a few lines of malicious code, they can silently skim payment card data, personal information, and login credentials as users interact with legitimate websites — often without anyone noticing.
In this blog, we’ll break down how digital skimming works, why it’s so dangerous, and what businesses and security teams can do to prevent it.
Magecart
Perhaps the best known type of digital skimming attack is called ‘Magecart.’ Magecart-style attacks are a type of threat in which financial transaction data (often credit card details) are intercepted by digital skimming the information from online payment forms. Although the name would seem to suggest a collective cybercriminal gang or a type of malware, the term ‘Magecart’ is actually just another name for a digital skimming attack.
For the past few years, Magecart-style breaches have been steadily on the rise. British Airways, Macy’s, Procter & Gamble, American Cancer Society, and many more have been Magecart victims. And these are just the high-profile breaches covered by the media. There are hundreds (if not thousands) of smaller scale e-skimming breaches happening daily that do not receive media attention.
Malicious Magecart-like code designed for e-skimming has been found in the Salesforce Heroku Cloud, in Amazon S3 buckets, Amazon CloudFront CDN, and other content delivery networks. Magecart digital skimming code has also been discovered impersonating a legitimate security firm, known as Sanguine Security, as a way to disguise itself.
Magecart e-skimming is a covert and a very real and present threat to both consumers and businesses.
Web Skimming Attacks
Web skimming attacks (sometimes also called formjacking) are a type of digital or e-skimming attack on modern web applications, websites, and mobile applications that contain compromised third-party JavaScript code. The malicious code gives attackers unrestricted access to sensitive data that they can sell later on in the dark web. Sensitive data includes:
- Credit/payment card information
- Billing information
- Financial records
- Login credentials such as user IDs and passwords
Threat actors have paid close attention to how easy digital skimming attacks are to deploy and how successful they have been. The main reason digital skimming is so simple is due to how vulnerable JavaScript code is to manipulation and obfuscation.
Over the past few years, skimmers (cybercriminals engaged in digital skimming attacks) have actively updated their techniques to better infiltrate changing technologies and take advantage of businesses that don’t stay on top of vulnerability management. Here are some of the most notable attacks and backdoors they have exploited over the last three years:
JavaScript Injection Attacks
During a JavaScript injection attack, a hacker gains website or web application parameter information and changes the values. This allows the threat actor to manipulate the website or application and collect sensitive data, such as personally identifiable information (PII) or payment information.
Hackers often find it easier to infect a third-party JavaScript code because this type of code is typically not part of internal security oversight. Third-party script can also run in the browser’s background with unrestricted access to sensitive data. Magecart criminals like to target popular third-party JavaScript libraries that enable typical website functionalities used by sales, marketing, customer support functions. These include chat bots, social media buttons, marketing analytic tools and trackers, digital ad retargeting, tag managers, and sign-up forms.
Drive-by Skimming
In drive-by web skimming, a threat actor compromises third- or fourth-party code with malware, with the hope that multiple organizations use this code and inadvertently infect their websites and web applications. Modern web applications load an average of over 20 third- and fourth-party scripts as part of the user experience. Because of this, compromising one of these third- or fourth-party elements with malicious JavaScript lets an attacker compromise multiple websites simultaneously.
By attacking third-party tools, hackers are also able to penetrate almost all the target businesses’ customers at once, gaining the same level of unrestricted access to their customer’s websites and the data. These types of attacks often hit thousands of companies at once.
Sideloading and Chain-loading Attacks
Sideloading and chainloading are attack techniques that allow the loading of malicious or infected JavaScript code onto a target webpage using legitimate scripts and tools. As an example, a group of threat actors known as “Magecart Group 12” breached over 300 e-commerce websites by adding e-skimming code to the Adverline JavaScript library, a third-party digital ad platform. Adverline’s retargeting script was then sideloaded with a digital skimming code, which in turn skimmed customer data and sent it to a Command & Control (C2) server. Sideloading-based e-skimming breaches can go undetected for long periods of time because infected code is loaded directly by web browsers well outside of the security perimeter that cybersecurity analysts are tasked with protecting.
Trusted Cloud-hosted Platform Skimming
E-skimming code has been found hosted by popular cloud platforms, including Salesforce Heroku, Amazon CloudFront CDN, and many others. Magecart e-skimmers were found following a spray and pray approach that targeted misconfigured Amazon S3 buckets. Skimmers were able to open backdoors to inserting malicious code into JavaScript libraries used by thousands of organizations.
Public Wi-Fi Skimming
IBM researchers discovered this type of e-skimming attack on public Wi-Fi hotspots. In a public Wi-Fi skimming attack, threat actors infiltrate a large number of users in public spaces, such as airports and hotels, by skimming off unprotected public Wi-Fi. Threat actors insert skimming code via Wi-Fi hotspots allowing them to exfiltrate the data users enter on web forms. These forms may include ecommerce checkout pages, marketing landing pages, or login pages. Public Wi-Fi skimming is quite a simple attack for threat actors to execute, since vulnerable Wi-Fi routers allow attackers to automatically inject skimming scripts into all websites accessed by users through their connected devices.
E-commerce Platform Skimming
Some of the world’s most popular e-commerce platforms like Volusion and Adobe Magento Marketplace have been breached by Magecart e-skimming code. These e-commerce platforms provide checkout services to thousands of merchants, while collecting and utilizing massive amounts of customer credentials, personal data, and financial information. Thousands of online stores were compromised during the Volusion platform hack in 2019 which went undetected for weeks.
Anti-forensic, Self-cleaning, and Stealth Data Skimming
There are a few variants of web skimming codes that are notoriously difficult to detect and remediate. Pipka is a web skimming code with anti-forensic, self-cleaning, and stealth capabilities. It is able to remove itself from a web page’s code after it has been executed, thereby making it exceptionally difficult to detect. Pipka-like threats require focused attention by cyber defenders and an automated scanning solution that alerts them to questionable code behaviors.
How to Defend Your Customers and Your Business
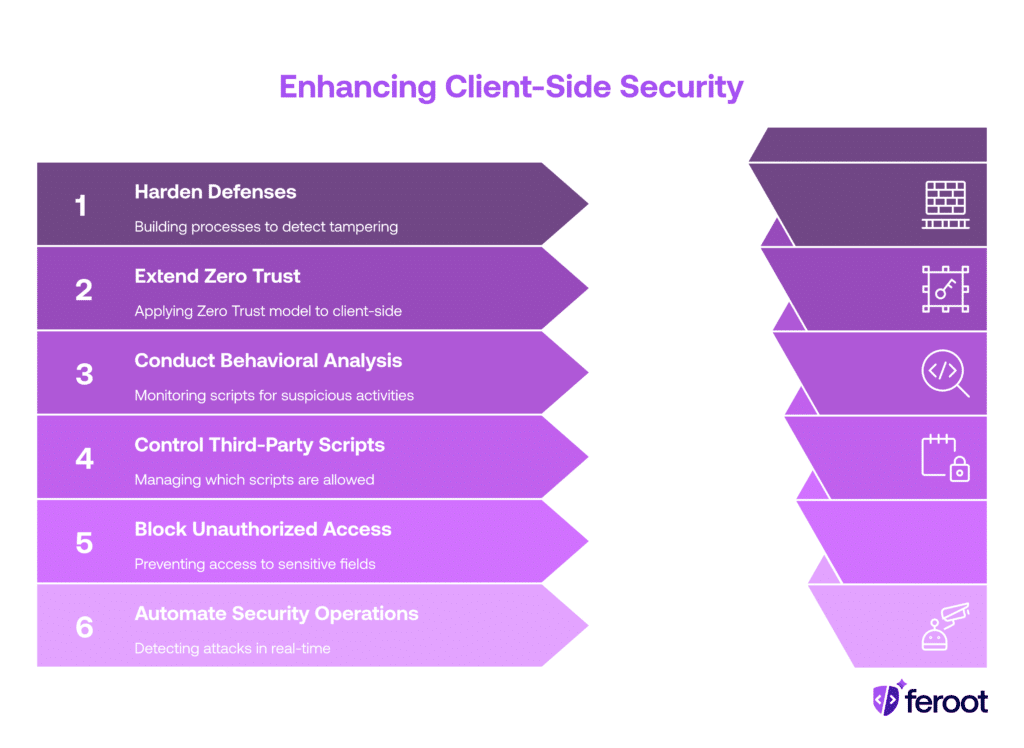
In order to defend your customers and your business from skimming attacks, security teams must implement the following six best practices for user-side security:
- Harden defenses by building processes and procedures to detect website and web application tampering. Keep track of your web assets and know if a change has been made to them at all times.
- Extend adoption of the Zero Trust model from the server-side to the client-side of your security program. The Zero Trust model is the best defense against web skimming attacks. Only those website scripts that need to have access to data should have access to data. Security teams can prevent vulnerable JavaScript from accessing sensitive data at the browser level if they control which scripts can access what data.
- Continuously conduct behavioral analysis of all scripts from the client-side to determine if there are any activities consistent with web skimming breaches, including:
- Access to form fields
- Sending of data from browsers to external servers
- Sideloading and chain loading of unauthorized JavaScript code
- Introduce central control over which third-party scripts are allowed to be loaded on each web page. Block and deny the browser from implementing unwanted sideloaded and chain loaded scripts.
- Block unauthorized JavaScript code from accessing sensitive form fields.
- Automate your client-side security operations to detect e-skimming attacks in real-time. Don’t rely on quarterly or annual vulnerability assessments alone. This allows threat actors to fly under the radar for months, thereby exposing your business to long windows of time for threat actors to skim data from you.
Sounds challenging, right? To be honest it is. Most companies cobble together a variety of tools such as vulnerability intelligence portals, vulnerability scanners, application security testing software and more. Then, they have to scan each web asset individually or write custom scripts in an effort to create some form of front-end security automation. This works in theory, but the behavioral analysis of the code likely will fall short.
There is a better way. Check out PaymentGuard. If you are interested in automating your client-side security operations and hardening your skimming defenses please don’t hesitate to reach out to us. Our client-side security specialists stand ready to help you protect your business and your customers. You can also request a demo via this link.
FAQ
What is a web skimming attack?
Web skimming, or formjacking, is a method where attackers inject malicious scripts into a site to steal data like credit card numbers or login credentials as users input them.
Why are skimming attacks hard to detect?
Most skimmers operate on the client side—inside the browser—where traditional server-side or perimeter security tools have no visibility. Hackers use obfuscation, trusted domains, and supply chain tampering to stay hidden.
Can these attacks affect compliance with PCI DSS or HIPAA?
Yes. PCI DSS 4.0 Requirement 6.4.3 and HIPAA privacy rules both require organizations to secure how user data is collected and transmitted. Skimming attacks can lead to serious compliance violations.
How can we protect against browser-side skimming attacks?
Use client-side security tools like Feroot that provide visibility into JavaScript behavior, detect unauthorized script changes, and map threats to compliance frameworks like PCI DSS and HIPAA.
Are third-party scripts a risk factor for skimming?
Absolutely. Many skimming attacks piggyback on third-party services or content delivery networks (CDNs). Even small script changes in analytics, ad tech, or plugins can open doors for attackers.





