You don’t have to dig far into a payment page before the pattern makes itself obvious. A few scripts are yours. A few belong to vendors you expected. But then the list keeps going, and you start to see something else.
What you will learn in this article
- Why 20-30% of payment page scripts come from fourth-party domains you never approved, and how script sprawl accumulates outside normal deployment pipelines
- Why traditional auditing methods miss conditional scripts that load only for certain regions, devices, or user segments, leaving PCI DSS 6.4.3 and 11.6.1 compliance gaps
- Step-by-step manual audit process: identifying payment surfaces, observing browser loads, classifying scripts, and building defensible inventories for QSA reviews
- How automated monitoring with PaymentGuard AI provides continuous visibility into runtime script behavior, detecting unauthorized changes immediately instead of weeks later
What else is running on your payment pages that you never saw?
Roughly 20 to 30 percent of the scripts come from fourth-party domains, i.e., your vendors’ vendors. These are the scripts that sit on domains no one recognizes. They carry tags that never go through review. And they sometimes pull in helpers who aren’t supposed to load anything at all.
But once the scope becomes visible, the rest narrows to one essential question: what else is running that we never saw?
This piece is about answering that question and discussing the steps of auditing a payment page in a way that finally reflects what the browser is actually doing.
Why is payment page script visibility hard
On paper, the payment page usually looks like one of the most controlled parts of the site. But in practice, it is often one of the least understood.
The problem is that much of what executes in the browser is assembled at runtime by a mix of internal code, vendor code, and vendor dependencies that sit outside normal deployment paths.
All of that adds up because of the nature of the environment. Scripts arrive from different owners, through different tools, and on different timelines. Some get deployed directly, some come through tag managers, and others appear as hidden dependencies of existing integrations.
And that is the real challenge, because you are trying to keep track of something that keeps shifting while you look at it.
How scripts multiply without approval
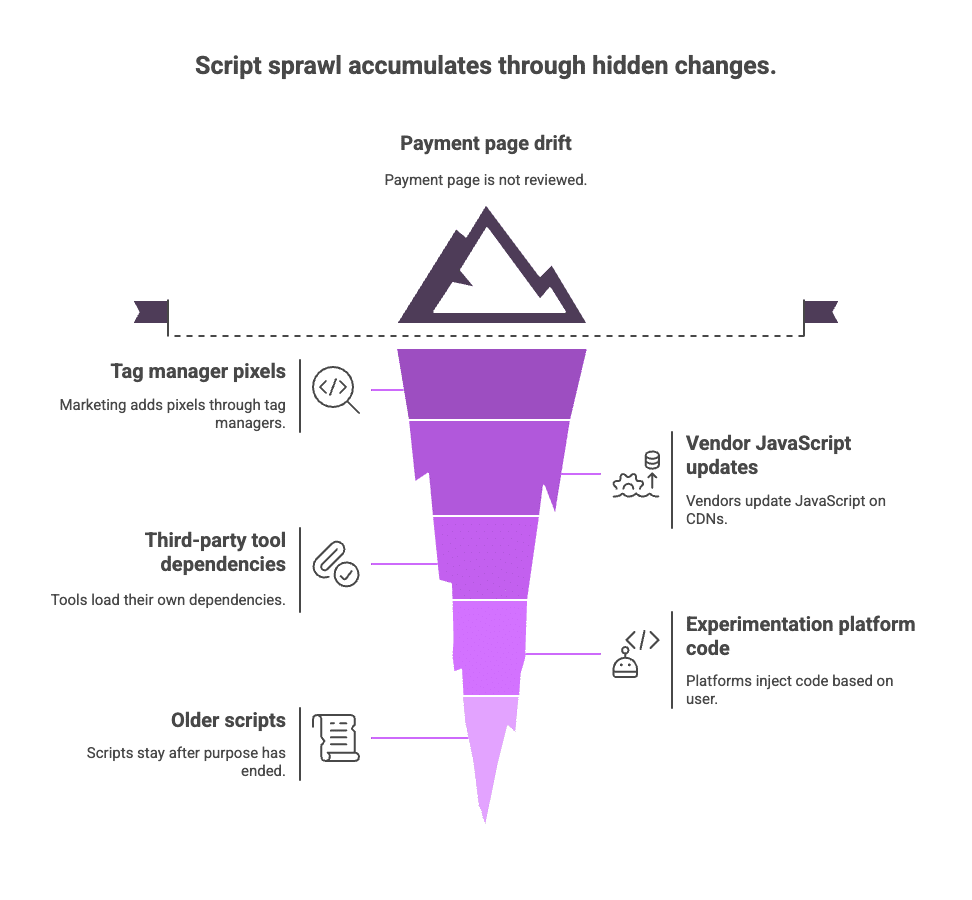
Script sprawl rarely comes from a single decision. It accumulates through normal operations. For example, marketing adds pixels through tag managers, and vendors update their own JavaScript on CDNs, and as that happens, those updates propagate without touching your deployment pipeline.
Then comes the third-party tools. They load their own dependencies, extending the chain beyond what you originally approved. Most of the experimentation platforms inject code based on who the user is and which variation they fall into. And older scripts from past campaigns or vendors often stay in place long after their purpose has ended.
Each change is small. None of it looks risky on its own. But together, these shifts add up, and over time, the payment page drifts into a state that no one explicitly reviewed or authorized.
Why traditional methods don’t see the full picture
Traditional methods fall short because they focus on what you deploy, not what the browser assembles at runtime. For example, you may ship the same code to everyone, but the browser can still load a different set of scripts based on region, device, or experiment, and the vendor URLs you trust can change their contents without notice, pulling in fourth-party dependencies you never reviewed.
So by the time the page renders, the DOM reflects changes made outside your release process.
The same limitation shows up in manual inspection. It shows one path on one device at one moment, but it cannot surface scripts that load only for certain regions, user segments, or experiment variations.
Point-in-time audits age as quickly because the browser environment changes independently of your deployment process. New tags appear as vendors push updates or third parties load additional dependencies. So point-in-time documentation goes stale.
To add to it, ownership gaps only widen the blind spots because responsibility for browser behavior gets distributed across several functions. When each team manages only the part it directly controls, and no team is accountable for how those parts combine at runtime, that fragmentation leaves no single source of truth for what the browser ultimately executes. That’s why traditional methods struggle to produce a complete view.
Requirements 6.4.3 and 11.6.1 only expose traditional methods further
Requirement 6.4.3 expects you to maintain a complete inventory of all scripts on payment pages, to authorize each one, and to document why it is necessary.
The intent is straightforward. PCI cares about what the browser actually renders, not what your deployment pipeline suggests should be there. And without visibility into that runtime reality, you simply cannot produce defensible evidence.
Getting that complete script view gives you a solid footing for the questions a QSA might ask, like:
- What scripts are running on your payment pages right now?
- Which ones have been explicitly approved?
- Who owns them?
- What data can they access?
- Why are they needed?
These questions reveal that payment pages are complex in a way that traditional controls were never designed to observe.
Manual vs. automated script auditing
Manual and automated script auditing differ in what they can realistically keep up with. Manual reviews rely on a single load of the page. They show what runs in that moment, but they struggle with scale, timing, and consistency.
On the other hand, automated discovery starts from the opposite premise. It monitors the browser continuously, tracks changes as they occur, and stays aligned with the shifting set of scripts that modern payment pages assemble at runtime.
Those different starting points lead to different strengths. And the contrast becomes clear across a few core factors:
| Factor | Manual Audit | Automated Discovery |
| Time to complete | Days to weeks | Hours |
| Scripts discovered | Partial, misses dynamic and conditional loads | Complete across all execution paths |
| Classification accuracy | Requires manual research | Automated first-, third-, and fourth-party tagging |
| Currency | Stale within days | Continuously updated |
| Repeat effort | Full re-audit each time | Ongoing monitoring |
| Developer resources | High | None |
The takeaway is simple: if the page keeps changing, the audit method has to keep pace, and automated auditing is built for that.
How to audit Payment Page Scripts (Step-by-Step)
There are two ways to audit a payment page: either manually or through automated discovery. Manual reviews give you a direct look at what the browser loads, but only at that moment. Payment pages shift often because vendors update code, tag managers add new tags, and scripts load conditionally, so the snapshot goes out of date quickly.
Automation approaches the same surface from a broader angle and follows how the script set changes over time. Both paths have value, and it helps to walk through each one.
The Manual Path to Auditing a Payment Page: Step-by-Step
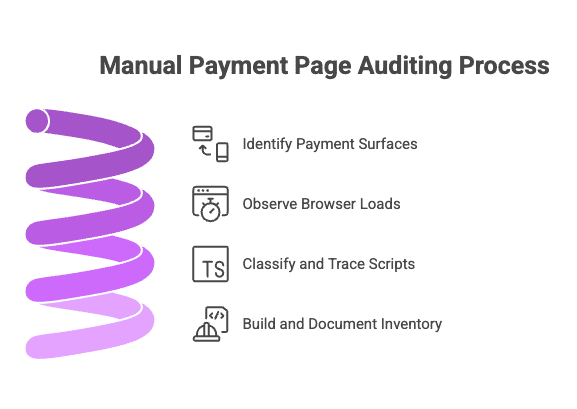
Step 1: Find every payment surface.
You identify every place where payment data appears. To do that, checkout flows, saved-card pages, subscription updates, embedded widgets, and iframes are all part of the surface that needs to be mapped, because the browser treats each of them as extensions of the same payment experience.
Any script running on these pages can reach the same data, so they belong in scope from the start.
Step 2: Observe what the browser loads.
Here, you load the page and watch what the browser pulls down. Then you run the flow again in a different browser or as a different type of user, because the script set shifts with even small changes in context.
Eventually, you might hit a wall due to limitations. That’s because no matter how many passes you make, you only see the paths you manage to trigger. The browser loads different scripts for different regions, devices, experiment buckets, and marketing segments, so some behavior simply never appears in a manual run.
When that happens, simply take the view you did get and move forward, knowing it is incomplete by design and that the next step is to make sense of what you could capture.
Step 3: Classify and trace the scripts.
You separate first-party from vendor scripts, then follow the trail of unfamiliar domains. Some origins are obvious. Others might require digging to understand who owns them and what they touch.
Know that fourth-party chains often emerge here, and they rarely come with documentation.
Step 4: Build and document an inventory that you can defend
Everything gets documented into a defensible trail in this step. And that should include source, purpose, owner, and whether the script has a clear business reason to exist.
Know that QSAs might flag the unknowns, so keep them on your review list. Note down unnecessary legacy scripts for removal. And in the end, you’ll get an inventory that reflects what you saw, organized tightly enough to satisfy an internal review.
Now let’s talk about the second option, the automated path to auditing scripts.
The Automated Path with PaymentGuard AI
Step 1: Deploy PaymentGuard AI and begin monitoring
Getting started with PaymentGuard AI is straightforward. You add a lightweight snippet to your payment pages, and that is usually all that’s needed.
Within a few minutes, PaymentGuard AI begins watching what the browser loads in real time. By the end of the first day, it captures the script activity that manual audits struggle to surface.
Step 2: Review the inventory that the system builds for you
Once monitoring is live, the inventory starts to take shape on its own. Every script that executes on your payment pages appears in one place.
PaymentGuard AI classifies them automatically into first, third, and fourth-party, shows the domains they call, and outlines what data each script can access. Anything unusual or new is flagged, so you don’t have to go hunting for it.
Step 3: Spot what shouldn’t be there
From this step, automation moves you from discovery into control. PaymentGuard AI takes the full script set it observes in the browser and immediately shows you what needs attention.
This way, anything without an approval record is surfaced first. It calls out anything new that comes up since the last review. And any script that interacts with payment fields gets highlighted so you can assess its intent quickly.
The system also traces the dependency chain for each script. If a marketing tag pulls in a helper library, and that helper loads yet another dependency, PaymentGuard AI traces that chain automatically. So you see not just what appeared on the page, but which script introduced it.
Step 4: Move decisions into a clear, repeatable workflow
PaymentGuard AI assigns each script an owner, a justification, and an approval record as part of normal operation. Anything that is not authorized is surfaced so it can be flagged, investigated, or removed.
Because this happens continuously, the system maintains integrity in real time instead of forcing teams to rebuild the truth at audit time. This way, when a QSA asks for evidence, it is already in place.
FAQ: Payment page script auditing
How often should we audit payment page scripts?
The frequency depends on how your payment pages change. Organizations with active marketing campaigns or frequent vendor updates benefit from continuous monitoring rather than periodic audits. Manual audits typically run quarterly at minimum, but by the time you complete one, the script landscape has often shifted. PCI DSS 11.6.1 requires detection mechanisms that can identify unauthorized changes as they occur, not weeks or months later. The more your payment pages evolve, the more continuous visibility matters.
What should we do if we discover unauthorized scripts during an audit?
Start by identifying the script’s source and purpose. Trace whether it came through your tag manager, a vendor update, or as a dependency of an approved script. If the script serves no documented business purpose or accesses payment data without authorization, remove it immediately. If it appears to serve a legitimate function, document that function, assign an owner, get formal approval, and update your inventory. The key is moving from discovery to a documented decision quickly, not letting unknowns linger.
Can we rely on browser developer tools for payment page audits?
Browser developer tools show you what loads in a single session, which is valuable for spot checks. But they miss scripts that load conditionally based on region, device type, user segment, or experiment variation. They also require manual effort to classify scripts, trace fourth-party dependencies, and maintain documentation. Developer tools are useful for initial investigation, but they cannot provide the continuous, comprehensive view that PCI DSS requirements expect for production payment pages.
Do all third-party scripts on payment pages need formal approval?
Yes, under PCI DSS 6.4.3. Every script that executes on a payment page must be authorized, justified, and documented. This includes first-party scripts you developed, third-party vendor scripts, and fourth-party dependencies that vendors load. The requirement is clear: if a script can access payment page content or transmit data off the page, it needs to be in your inventory with a documented business justification and an assigned owner.
How do we handle scripts that only load for certain users or regions?
This is where manual audits struggle. A script that only loads for users in certain experiment buckets or geographic regions will not appear in every session. You need monitoring that covers all execution paths, not just the ones you happen to trigger during testing. Automated discovery solves this by observing all runtime variations continuously. If you are using manual methods, document known conditional scripts separately and test multiple user contexts, but recognize this approach leaves gaps.
What happens between audits if we only review scripts quarterly?
Payment pages change constantly. Vendors push JavaScript updates to their CDNs without notification. Marketing teams deploy new tags through tag managers. Third-party scripts load new dependencies. Between quarterly audits, your script inventory drifts from reality. By the time the next audit happens, you are documenting a script landscape that has already changed. This creates compliance risk because you cannot answer what is running right now. Continuous monitoring closes that gap by keeping the inventory current between formal reviews.
What do QSAs actually look for during payment page script audits?
QSAs want evidence that you know what scripts run on payment pages, that each one has been authorized with a documented business justification, and that you can detect unauthorized changes. They typically ask for a complete script inventory, approval records for each script, evidence of continuous monitoring per 11.6.1, and documentation of how you handle newly discovered scripts. Point-in-time spreadsheets from months ago do not satisfy these requirements. QSAs want to see that your controls reflect current reality, not historical snapshots.
Can we just block all third-party scripts to simplify compliance?
You can, but most organizations rely on third-party tools for fraud detection, analytics, payment processing, and customer experience features. Blocking everything creates operational problems without solving the underlying issue. The better approach is controlling which scripts load, documenting why they are necessary, and monitoring their behavior continuously. PCI DSS does not require eliminating third-party scripts. It requires knowing what they do, authorizing them explicitly, and detecting when something unauthorized appears.
What is the difference between third-party and fourth-party scripts?
Third-party scripts come from vendors you have a direct relationship with, such as your analytics platform, fraud detection tool, or chat widget provider. Fourth-party scripts are dependencies that your third-party vendors load without your direct knowledge or approval. For example, if your fraud detection script loads a helper library from a different domain, that helper is a fourth-party script. PCI DSS 6.4.3 requires you to inventory and authorize both. Fourth-party dependencies are often the biggest blind spot in manual audits.
How does automated monitoring handle scripts that change frequently?
Automated monitoring tracks the script set continuously, so when a vendor pushes an update or a tag manager deploys a new pixel, the system detects the change immediately. It compares the new script against your approval inventory, flags anything unauthorized, and updates the record for scripts that were already approved. This means your inventory stays current without requiring manual re-audits every time something shifts. The monitoring adapts to the pace of change that payment pages actually experience.
We have multiple payment flows across different domains. Do we need separate audits?
You need comprehensive coverage across every payment surface where card data appears. This includes primary checkout flows, subscription update pages, saved payment method screens, and any embedded payment widgets or iframes. Each surface can load a different set of scripts, so they all belong in scope. Manual audits require separate reviews for each domain and flow. Automated monitoring can cover all surfaces from a single deployment, providing unified visibility without multiplying audit effort.
Moving from point-in-time audits to ongoing control
An audit gives you a snapshot, but it does not give you ongoing reliability. Scripts shift with every campaign, every vendor release, and every quiet tag manager update. If you are not watching the browser continuously, your inventory drifts and your hard-won visibility fades.
PaymentGuard AI turns that drift into something you can manage. It keeps the script inventory current, detects new behavior the moment it appears, and ties every change back to an owner and a justification. With it, you get a control surface that matches how modern payment pages actually work: dynamic, distributed, and always in motion.
CTA: Ready to see what’s actually ruņning on your payment pages? Meet with a Feroot expert who will listen to your business needs and provide full visibility into the Feroot AI platform.