Think of your website as the front desk of your clinic. You wouldn’t let vendors set up recording equipment in your waiting room without contracts. But that’s precisely what happens when tracking pixels, session replay, and chat tools run on patient-facing pages without Business Associate Agreements.
What you’ll learn in this article:
- The Office for Civil Rights’ 2024-2025 spotlight is on browser-based website tracking tools, now driving significant HIPAA enforcement actions
- HIPAA violation penalties still range between $141-$2,134,831 per violation category/year, and website violations multiply fast across pages, tools, and time
- Continuous client-side monitoring is now table stakes to avoid penalties tied to analytics, pixels, and session replay
In 2025, the OCR sent a clear message: HIPAA enforcement now targets the browser. The OCR collected over $9.9 million in penalties across 22 actions from healthcare organizations in 2024. These penalties were all due to hidden data flows from website tracking tools.
Even compliant servers cannot offset non-compliant websites. In 2025, the highest risk often starts where marketing meets healthcare: within the patient’s browser.
HIPAA penalty tier structure
Penalties under HIPAA compliance are tiered based on an organization’s degree of culpability. In 2025, the OCR expects active due diligence from healthcare companies, especially when clients’ websites process or handle patient data.
The four penalty tiers
| Penalty Tier | Level of Culpability | Minimum Penalty / Violation | Maximum Penalty / Violation | Annual Penalty Limit (per identical violation category) |
| Tier 1 | Reasonable efforts to comply | $141 | $71,162 | $2,134,831 |
| Tier 2 | Lack of oversight | $1,424 | $71,162 | $2,134,831 |
| Tier 3 | Willful neglect, but corrected within 30 days | $14,232 | $71,162 | $2,134,831 |
| Tier 4 | Willful neglect, not corrected within 30 days | $71,162 | $2,134,831 | $2,134,831 |
Why the revised tier structure matters
Per-violation fines can add up quickly if multiple records or pages are affected, and the ~$2.13 million cap underscores the significance of large-scale tracking failures.
Failing to monitor client-side scripts or to enforce tag manager governance is now considered willful neglect under Tier 4, the most serious penalty classification.
Why website violations dominate 2025 enforcement
Beginning in late 2022, the OCR issued guidance on tracking technology penalties, with updates in 2024 and renewed scrutiny in 2025.
For example, one measurement study found that 72.6% of 40,150 websites had Google trackers configured, and 11.6% of Meta trackers were set to collect form data that could include health information. Another analysis revealed that a third of major U.S. hospital websites still had the Meta Pixel installed in 2024.
OCR’s 2022-2024 bulletins make clear that using tracking technologies in a way that results in disclosures of PHI to third-party vendors may count as impermissible disclosure under the Privacy Rule. Regulated entities that continue these practices risk being viewed as showing “willful neglect.”
Unlike obscure server breaches, web-based tracking misuse leaves footprints, browser audits, vendor packet captures, or consumer complaints. OCR and its joint letters with the Federal Trade Commission (FTC) have emphasized this traction.
Website tracking that collects ePHI can affect thousands or millions of visitors and often involves highly sensitive conditions. The scale and sensitivity amplify enforcement risk.
Because website tracking violations combine broad exposure, measurable evidence, and more explicit regulatory expectations, they frequently trigger the OCR’s higher-tier HIPAA violation penalties.
Major website-related enforcement actions
Over the past two years, regulators and courts have treated website tracking on health properties as a regulated data flow. Even when no Electronic Health Record is collected, pixels, analytics, session replay, and chat tools can expose PHI through page context, inputs, and event streams. Here are some examples.
BetterHelp – FTC order
The Federal Trade Commission found that BetterHelp shared users’ health-related sign-up and intake information with advertising platforms (e.g., Meta, Snapchat) for marketing purposes. They incurred $7.8M in redress, strict bans on using health data for ads, and required notice and deletion/limitation obligations.
The key takeaway is that marketing pixels on sensitive funnels are high-risk without explicit, compliant authorization and tight controls. The repercussions go beyond fines and include reputational damage, business disruption, and additional work for the company.
General U.S. Healthcare Sector
Widespread use of tracking pixels (e.g., Meta/Facebook Pixel) and similar tools on healthcare websites was transmitting health-related data without sufficient controls. Industry reporting cites $100M+ in penalties and settlements tied to pixel-tracking violations during 2023–2025.
Pixels and related scripts captured page context, events, and identifiers across patient-facing pages. Without governance and monitoring, those signals flowed to third parties beyond permitted HIPAA uses.
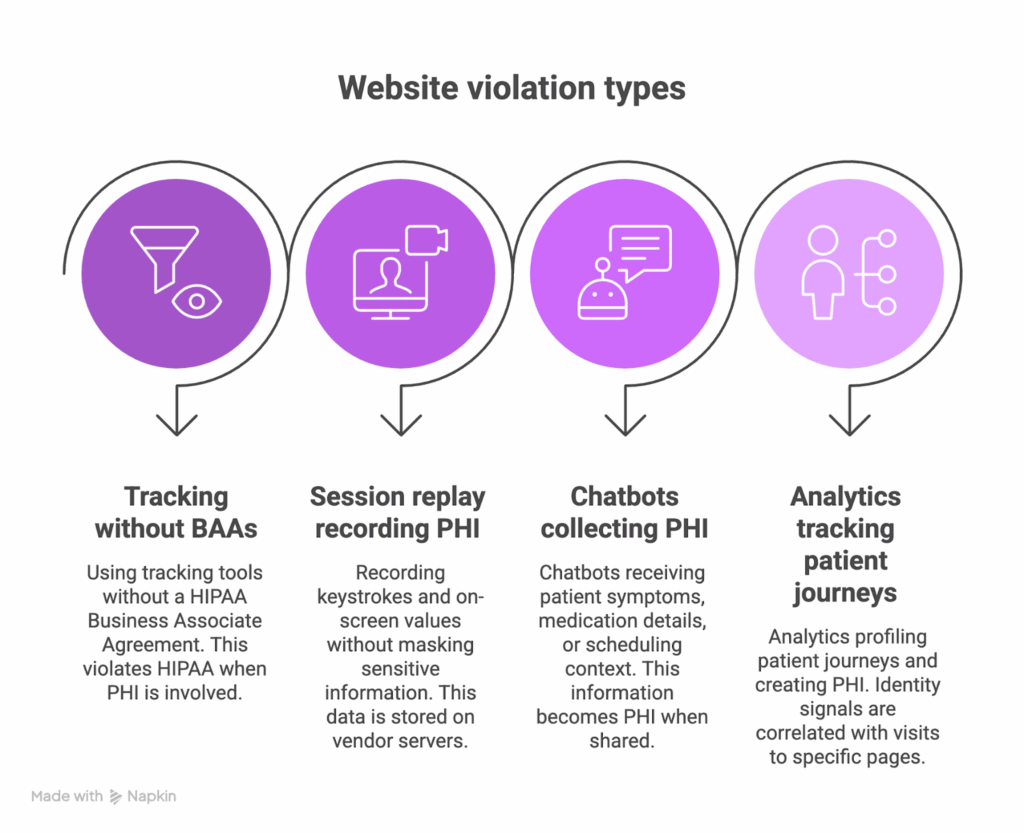
Top website violation types OCR targets
Across investigations, the patterns are consistent: website HIPAA violations usually start with ordinary tools deployed without governance. Here are the four most common HIPAA violations on websites and how to prevent them.
1. Tracking technologies without BAAs
Standard tools like Google Analytics and Meta Pixel often run on patient-facing pages, but neither vendor signs a HIPAA Business Associate Agreement for these products. HIPAA, however, expects a BAA whenever a vendor creates, receives, maintains, or transmits PHI on your behalf.
That leaves healthcare organizations with a hard trade-off: either keep these pixels completely off any journey that can involve ePHI (portals, scheduling, symptom checkers, bill pay, refills), or remove the pixels entirely from regulated flows. Many teams feel it’s “not realistic” to omit Google or Meta tags altogether, which is exactly where complexity and risk creeps in.
If a tool can receive identifiers tied to care (cookies, device IDs, email hashes, account IDs) plus health context (conditions, appointments, payments), treat it as a de facto Business Associate. If the vendor won’t sign a BAA for that product, your only defensible options are to:
- Keep it out of ePHI journeys, and
- Prove that no PHI reaches the vendor through URLs, events, query params, or pixels.
2. Session replay tools recording PHI
Platforms like Hotjar or FullStory record keystrokes, form entries, and on-screen values on appointment, portal, or intake pages, often without field masking enabled, and store these recordings on the vendor’s servers.
The practical baseline is simple: don’t run replay on any page that can capture ePHI, unless you’re using a HIPAA-eligible product that will sign a BAA and you’ve verified masking, retention, and scoping in practice. Even then, keep replay narrowly scoped to specific UX questions, default to redaction for health-related fields, and re-test masking regularly with documented sessions.
3. Chatbots collecting PHI
Widgets like Intercom or Drift often receive symptoms, medication details, or scheduling context. Once a patient shares this information in chat, it becomes PHI and is sent to a third-party platform. Treat them as part of your HIPAA surface.
Implement a BAA, restrict the bot to non-PHI tasks (e.g., hours, locations, and billing FAQs), or route any health questions to covered channels, such as secure messaging within the patient portal.
4. Analytics tracking patient journeys
Analytics can profile patient journeys in ways that create PHI. When identity signals such as IP addresses, device IDs, or login states are correlated with visits to condition-specific pages, the vendor receives health-related data tied to an individual.
The remedy is to block analytics on PHI paths, enforce IP anonymization, and implement field-level blocking. Also, re-verify after every tag change and keep evidence of the controls.
Website violation penalty calculations
The U.S. Department of Health and Human Services’ Breach Notification Rule requires reporting breaches of unsecured PHI affecting 500 or more individuals within 60 days, and more minor breaches by year-end. The OCR’s public portal lists incidents that meet those reporting thresholds. Note that it isn’t a census of all website HIPAA violations or a determination of fines. Still, it is a solid compliance barometer and an excellent resource for teams tasked with deploying trackers.
How OCR actually calculates civil money penalties
HIPAA penalties are tiered and inflation-adjusted. OCR sets the per-violation range and an annual cap per violation category, then applies case-specific factors (e.g., the nature/extent of the violation and harm, organization size/resources, and mitigation).
OCR has emphasized risks posed by online tracking technologies; disclosures of PHI via pixels, session replay, analytics, or chat tools can trigger investigations, corrective action plans, and monetary settlements, especially when risk analysis, BAAs, or technical safeguards are lacking.
Beyond OCR penalties – Total costs
Class actions (separate from OCR), like Pixel/analytics lawsuits, have produced multi-million-dollar settlements.
Breach notification + response
Healthcare remains the highest-cost industry for data breaches; IBM’s 2024 report shows an average of $9.48 million per healthcare breach (all-in cost). That’s more than double the cross-industry average and highlights the downstream expense once data leaves your control.
Corrective Action Plans (CAPs)
When OCR enters a resolution agreement, CAPs often impose multi-year obligations, such as policies, technical remediation, workforce training, reporting, and monitoring. An example is the two-year CAP with the City of New Haven.
It means the fix isn’t a one-and-done. A CAP is a multi-year program that focuses teams on steady improvements: drafting and enforcing policies, closing technical gaps, delivering regular training, and reporting progress on a set cadence. Day to day, it raises the bar on governance of data flows, including third-party scripts, pixels, and tags, until continuous monitoring is demonstrable. Staying on schedule simplifies oversight and builds durable HIPAA compliance capabilities, making marketing operations more predictable.
Operational remediation
Post-incident work commonly includes: removing or re-configuring trackers across all web properties, implementing client-side monitoring, renegotiating BAAs with web vendors, and tightening consent controls.
The OCR’s tracking-technology bulletin (updated June 26, 2024) underscores that when PHI is disclosed via online trackers, HIPAA rules apply and BAAs or authorizations are required.
Reputation and patient trust
Media coverage and targeted-ad complaints fuel scrutiny. The OCR has prioritized Security Rule compliance in investigations involving tracking technologies. Expect sustained oversight and reputational drag until controls are verified and documented.
A website violation that gets hundreds of thousands of visitors can quickly compound.
The reliable way to reduce this risk is to prevent disclosures at the source: inventory scripts, lock down allowed domains (CSP/SRI), and continuously monitor client-side behavior in alignment with HIPAA guidance on tracking technologies.
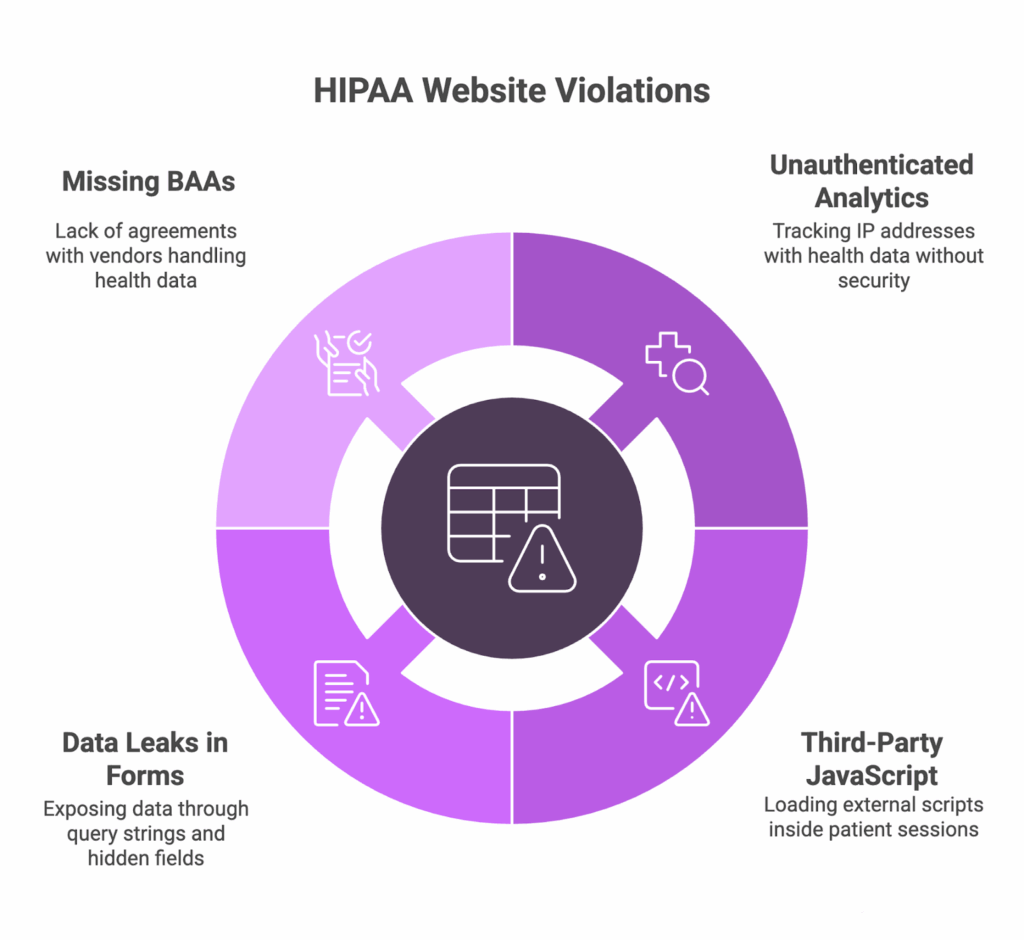
The most common HIPAA website violations
In our experience, the same patterns keep surfacing:
- Unauthenticated pages run analytics that combine IP addresses with health-related browsing, creating PHI without safeguards
- Authenticated portals load third-party JavaScript (tags, chat, A/B tools) inside the patient session
- Contact and appointment forms leak data to analytics or pixels via query strings, hidden fields, or session-replay capture
- BAAs are missing or incomplete for core web vendors like hosting, analytics, chatbots, and CDNs
Frequently Asked Questions
We use Google Analytics. Does that automatically make us non-compliant?
Not automatically, but Google doesn’t sign BAAs for standard Google Analytics (GA4 or Universal Analytics). If GA is running on pages where it could access PHI (e.g., patient portal URLs, appointment pages, health condition searches), that’s likely an impermissible disclosure. Google does offer HIPAA-eligible services (Google Workspace, Cloud Platform), but not for Analytics.
How does OCR even find out about website tracking violations?
Multiple ways: patient complaints about targeted health ads, browser audits during investigations, vendor data-sharing disclosures, class-action discovery, and proactive enforcement sweeps. Unlike server breaches, web tracking leaves visible footprints in browser developer tools and network traffic.
If we remove the tracking tools now, are we protected from past violations?
Removing tools shows good faith and stops ongoing violations, but doesn’t erase past disclosures. OCR can still investigate historical incidents. However, prompt corrective action can reduce penalties (moving from Tier 4 willful neglect to Tier 3 if corrected within 30 days).
Our tracking vendor says they’re “HIPAA compliant.” Is that enough?
Not without a signed BAA for the specific service you’re using. Vendors can be technically capable of HIPAA compliance but not willing to sign BAAs for certain products. Always verify BAA coverage for your exact implementation.
Do cookie consent banners satisfy HIPAA requirements?
No. Cookie consent banners address privacy laws (GDPR, CCPA) but don’t satisfy HIPAA’s BAA requirements. Even if users consent to cookies, HIPAA requires either a BAA with the tracking vendor or a valid HIPAA authorization that meets specific requirements under 164.508.
Feroot’s path to HIPAA-ready website compliance
If 2024 was a warning shot, 2025 is the lesson. Your website is part of your regulated environment. OCR’s focus on tracking technologies closes a gap most programs have never addressed.
In our experience, the organizations that avoid HIPAA violation penalties do three simple things consistently:
- They know which scripts run on patient-facing pages
- They have BAAs (or hard blocks) for every web vendor that could receive PHI
- They monitor the browser like any other system that handles ePHI
The next step for you should be to inventory all third-party code with the help of Feroot HealthData Shield AI. Here’s what it does:
- Automatically finds trackers on your site. It discovers online tracking technologies across your healthcare webpages and patient journeys.
- Locates PHI at risk. AI maps where protected health information can be captured (e.g., web forms, medical searches, scheduling flows).
- Blocks unauthorized access in real time. It detects and controls tracking technologies so PHI isn’t exposed as pages load.